Technical Growth Paths Built Around Modern Threat Response
Ever gotten a weird text from “Netflix Support” asking for your credit card? Or clicked on a suspicious file, only to realize two seconds too late that it wasn’t from your coworker? Threats like these used to be rare enough to laugh off. Now, they shape how businesses think, hire, train, and invest. In this blog, we will share how modern threat response is reshaping technical growth paths across industries.
The Security Mindset Isn’t Optional Anymore
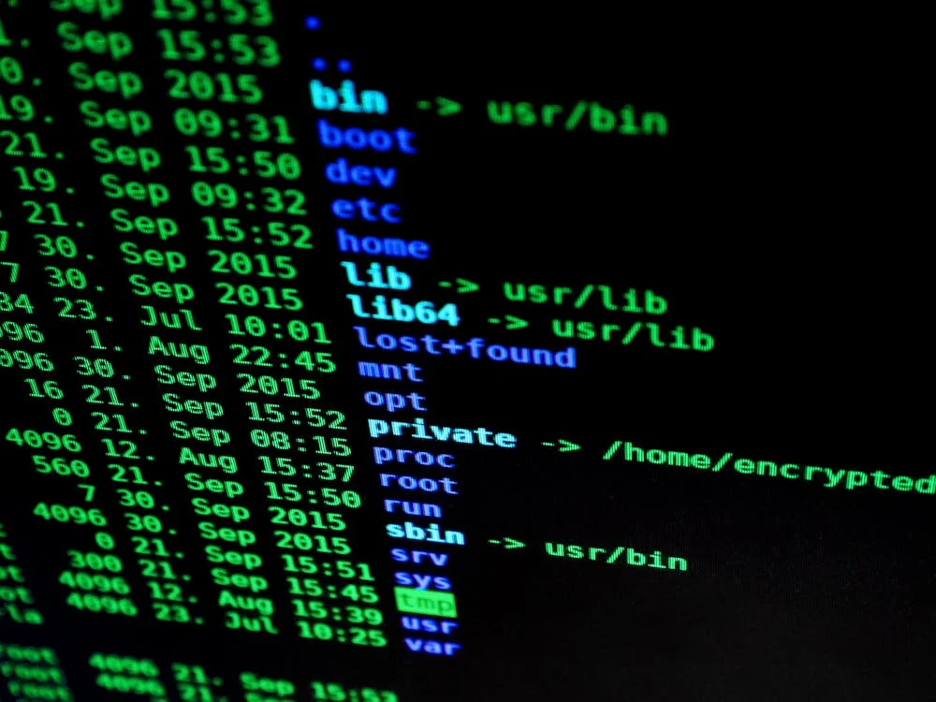
Cybersecurity no longer lives in the server room. It’s now a boardroom issue, a product design factor, a customer loyalty risk, and in many cases, a national concern. Threats aren’t just targeting systems—they’re targeting trust. When a ransomware group locks down a hospital, or when a phishing scam empties small business accounts, the damage isn’t just technical. It’s reputational, financial, and in some cases, life-threatening.
From retail to healthcare to fintech, companies are no longer asking whether they need security experts. They’re asking how fast they can build teams with real-world threat response skills. But this shift isn’t just about hiring more analysts. It’s about developing talent across technical tracks—engineers who know how to write secure code, network architects who can think like attackers, and cloud specialists who understand shared responsibility models.
For professionals looking to grow in this space, an online masters in cyber security degree offers a direct, flexible path into high-demand roles. These programs are designed not just to teach concepts, but to simulate threat environments and develop operational fluency. Graduates don’t just memorize frameworks—they practice detection, response, containment, and recovery in controlled environments that mirror what’s happening across sectors. And because the coursework stays tied to current events and evolving technologies, the learning stays relevant as threats evolve. As more organizations prioritize proactive security planning over reactive cleanup, this kind of preparation becomes a differentiator in the hiring process—and a safeguard for organizational resilience.
Cybersecurity isn’t a specialization anymore. It’s a foundational lens through which all modern tech roles are being redefined.
Growth Now Follows the Risk
Traditional technical growth used to focus on scope and stack. You became a senior engineer by solving bigger problems with more complex tools. You advanced by leading teams, writing cleaner code, or optimizing for speed and scale. Today, the ladder includes another dimension—threat awareness. Knowing how your system performs under attack isn’t niche. It’s table stakes.
This mindset shift is showing up in job descriptions. Engineers are expected to implement threat modeling into product design. DevOps roles increasingly require familiarity with intrusion detection systems. Even QA testers are being asked to simulate edge-case security failures. The question isn’t “Is this working?” anymore. It’s “Could this be exploited?”
As a result, the most valuable growth paths are now hybrid. Security engineers are learning how to code. Developers are learning incident response. Product managers are being trained to evaluate third-party risk. This blending of roles reflects the real-world demands of modern business, where security is everyone’s problem—even when it’s no one’s full-time job.
And because attackers don’t wait for budget cycles, companies are putting more weight on internal growth. Cross-training is on the rise. Internal labs, red team/blue team drills, and shared postmortem reviews help staff build skills without waiting for a breach to force the lesson. Organizations that invest in these programs build muscle before it’s tested under real pressure. They don’t just respond faster—they bleed less when hit.
Automation Is Good—Until It Isn’t
Every security team wants better tools. Endpoint protection platforms, SIEMs, firewalls with predictive threat scoring—it’s all helpful. But as automation expands, so does the illusion of safety. Many organizations assume that buying tech is the same as building capability. It isn’t.
What automation offers in speed, it often sacrifices in nuance. A well-tuned alerting system is great—until it triggers thousands of false positives and burns out your team. An auto-remediation tool can save time—until it breaks something critical because it didn’t understand business context. And AI-driven threat detection? Impressive, until attackers start feeding the models disinformation and gaming the logic.
This creates a need for security professionals who don’t just deploy tools—they understand their limits. They know when to escalate, when to override, and when to build fallback protocols. Technical growth in threat response isn’t about knowing the latest acronym. It’s about judgment, timing, and operational awareness. It’s about treating automation as a force multiplier—not a substitute for thought.
That’s also why mentorship is returning as a core part of technical development. Experienced engineers with breach scars are now seen as strategic assets, not just old-school holdouts. They’ve seen what happens when dashboards miss the real problem. They’ve sat in incident war rooms. They know how to move in the gray areas between playbooks. And they can train others to respond with the right mix of urgency and restraint.
Threat Response as a Business Language
Security is now baked into business continuity planning. It affects mergers, vendor decisions, insurance coverage, and market expansion. That means technical teams need to learn to speak the language of business risk.
A security lead who can explain exposure in terms of revenue impact becomes indispensable. An engineer who can quantify the cost of downtime builds stronger cases for infrastructure upgrades. Even frontline support teams are being trained to identify social engineering attempts and escalate without delay.
The New Value of Failure
One of the least talked about but most critical parts of technical maturity is knowing how to fail gracefully. Because no matter how good your systems are, something will go wrong. The difference is whether your organization learns or lurches.
Modern threat response includes recovery planning. It includes communication strategy. It includes knowing how to contain damage, restore operations, and investigate cleanly without spinning into blame. Teams that grow through real or simulated failures develop better instincts. They stop chasing perfection and start designing for resilience.
This also rewires company culture. When failure is viewed as proof of incompetence, no one speaks up. When it’s viewed as an opportunity to sharpen, teams move faster, report earlier, and prepare smarter. Technical growth that’s grounded in post-incident learning becomes more practical, more humble, and more durable.
So the question isn’t whether your career will involve a major threat. It’s whether you’ll come out of it sharper, wiser, and more valuable than before.
Modern threats aren’t going away. If anything, they’re getting more creative, better funded, and harder to predict. But companies—and individuals—who invest in meaningful technical growth don’t wait for the next crisis to prepare. They build paths that aren’t just technically sound, but threat-aware, responsive, and adaptable in real time. That’s where the real value lives now. In the messy, high-stakes space where engineering meets uncertainty—and shows up ready.
- IT Security
